GitHub Advanced Security Feature Comparison
A feature comparison between GitHub Enterprise, GitHub Enterprise with GitHub Advanced Security (GHAS), and Public Repos on github.com
Overview
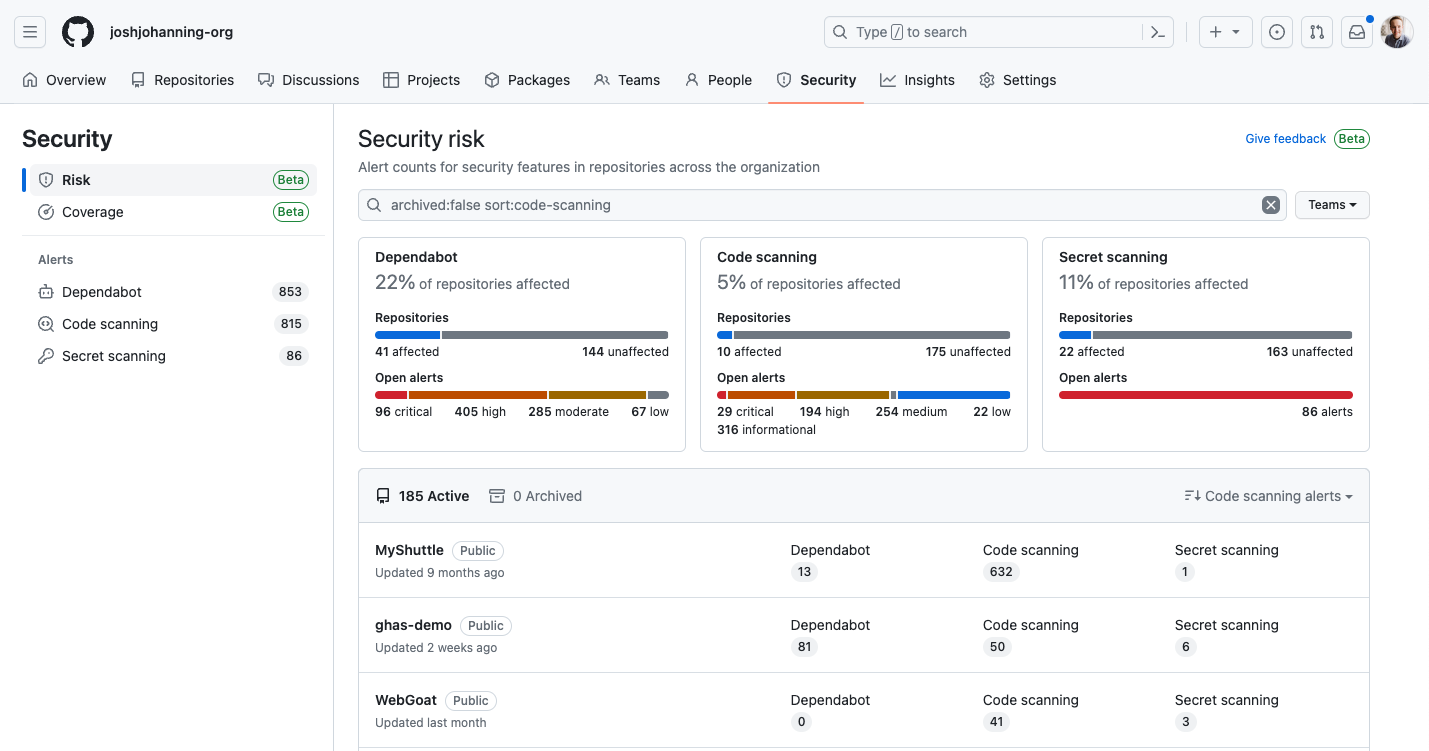
GitHub Advanced Security (GHAS) is an addon for those on GitHub Enterprise. While it costs extra, the code scanning, secret scanning, and the dependency review feature set is quite impressive. Nearly all of these features are enabled by default for Public Repos hosted on github.com (with the exception of the security overview, push protections for secrets, and custom patterns for secret scanning), so you can easily create a repo with some sample code from your personal GitHub account to play around with the features.
Follow updates in the Changelog blog for the latest updates on GitHub Advanced Security!
See also: GitHub Advanced Security Permissions Chart
GitHub Advanced Security Feature Comparison
I made this chart a while back for a client when helping them determine if the GHAS addon was worth it to them:
Notes:
- GHE = GitHub Enterprise
- GHAS = GitHub Advanced Security
- This chart primarily focuses on GitHub Enterprise Cloud, but note that Advanced Security is available for GitHub Enterprise Server 3.0 or higher. There may be slight differences in the features available for GitHub Enterprise Server based on the version
About Dependabot
There are a few components of Dependabot, and while I tried to list each feature individually in the chart, I wanted to call out a helpful quote of the documentation to help describe part of the differences between version updates and security updates:
About Dependabot version updates:
When Dependabot identifies an outdated dependency, it raises a pull request to update the manifest to the latest version of the dependency. For vendored dependencies, Dependabot raises a pull request to replace the outdated dependency with the new version directly. You check that your tests pass, review the changelog and release notes included in the pull request summary, and then merge it. For more information, see “Enabling and disabling Dependabot version updates.”
If you enable security updates, Dependabot also raises pull requests to update vulnerable dependencies. For more information, see “About Dependabot security updates.”
When Dependabot raises pull requests, these pull requests could be for security or version updates:
- Dependabot security updates are automated pull requests that help you update dependencies with known vulnerabilities.
- Dependabot version updates are automated pull requests that keep your dependencies updated, even when they don’t have any vulnerabilities. To check the status of version updates, navigate to the Insights tab of your repository, then Dependency Graph, and Dependabot.
Dependabot version updates requires creating a dependabot.yml configuration file in your repository whereas Dependabot security updates automatically locates supported package manifest files and alerts you when it contains vulnerable dependencies.
Dependabot version updates supported package ecosystems differs from that of Dependabot security updates.
Changelog
| Date | Note |
|---|---|
| Apr 26 2023 | Removing subscript note on secret scanning for public repos, added SBOM generation |
| Oct 11 2022 | Removing Beta from Security Overview for the Org, Security Overview is available to all GitHub Enterprise customers |
| Apr 06 2022 | Adding Dependency Review Action (Beta) |
| Apr 04 2022 | Adding Secret Scanning - Push Protections (Beta) |
| Mar 07 2022 | Adding new Security Overview for the Enterprise (Beta) and secret scanning note for public repos |
| Jan 26 2022 | Adding Dependabot section, reorganized chart |
| Dec 03 2021 | Initial post |